
The history of cryptography has evolved from ancient times. But understanding history helps us understand where we are now.
Many forms have existed such as:
- Egyptian hieroglyphs
- Phaistos disc
- Hebrew’s Atbash
- Scytale
- Caesar Cypher
- Vigenere
- Vernam Cypher
- Enigma
- Lucifer/DES
- Diffie-Helman
- RSA
- PGP
The purpose of cryptography is the art of secret writing. To speak the same language we must have the same definitions to terms I’ll be writing about.
- Algorithm – Mathematical techniques that are applied to do the substitution of transposition
- Cryptosystem – Is a combination of algorithm and cryptographic keys used to encrypt and decrypt the data.
- Work Factor – States how hard it would be to break the cryptosystem. Tested by cryptoanalysts.
- Encryption/Encipher – Conversion of plain text information into cipher text.
- Decryption/Decipher – Conversion of cipher text to plain text.
- Key – Encrypts and decrypts information. The more bits the key the bigger the key space. Some systems use more than one key known as key clustering.
Kerkchoffs principle is that someone can have public knowledge of the cryptosystem and the algorithm can still be secure.
Substitution cipher replaces bits, characters or blocks of characters with alternate ones.
Transposition cipher is where the position of a letter or of a binary digit is moved.
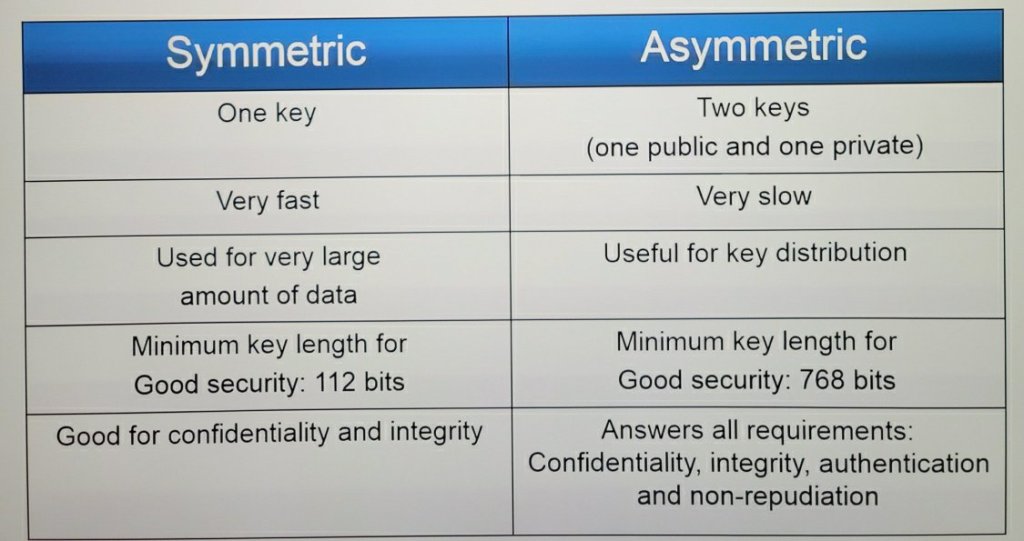
Symmetric Key Cryptography is a single key that encrypts and decrypts the data. It uses 128 bits and is very fast at encryption and decryption. Does not provide authentication or non-repudiation.
There are different algorithms used in symmetric key cryptography.
1. Block cipher – Blocks undergo a series of substitutions. Very time consuming and used mostly for storage of data.
2. Stream cipher – Data is treated as a stream and is encrypted one bit at a time while streaming. This makes it good to use for data in transit.
Data Encryption Standard (DES) is a symmetric algorithm that uses 64 bits for input and output and was broken into in 1998.
DES operates in native mode called the electronic code book. The theory was that data was broken into unique blocks using the same key and same method. Break one, break them all.
Another mode DES can operate is cipher block chaining where the plain text data is put into blocks and before encryption additional data is injected known as the initialization vector.
Double DES was then created to provide enhanced security. It used two 56 bit keys to give it a double work factor but still had the same strength as DES.
3DES was then born to use three 56 bit keys for an effective key length of 112 bits.
Rijandel was created to provide even more security. Two Belgian cryptographers, Joan Daemen and Vincent Rijmen created block ciphers that ranged from 128 to 256 bits.
The Advanced Encryption Standard (AES) was based off the Rijandel algorithm using a fixed 128 bits with key length of 128, 192, or 256 bits and was selected by NIST to replace DES.
Asymmetric key cryptography uses 2 keys. One key is a public and the other is a private key. If you encrypt data with the public key, only the private key can decrypt the data. Imagine it was your postbox, the mailman can drop off the mail (public key) but only you open the box (private key). This covers confidentiality, integrity, authentication and non-repudiation.
Diffie-Helman is a asymmetric key exchange algorithm used to exchange encryption keys that allows establishment of a shared secret key over an insecure communications channel using the discrete logarithm problem.
Hybrid cryptography is a mix of public key and symmetric key cryptography. Key distribution is done through public key cryptography. Asymmetric key algorithm is used to encrypt and communicate a session key. Symmetric key algorithm is used encrypt the data using the session key.
There is also cryptography in protocols. The Secure Socket Layer (SSL) enables secure communication between a client and a server. This was replaced by Transport Layer Security (TLS). TLS is mostly used in HTTP and converted it to HTTPS to identify a site is using a secure protocol.
Hashing functions takes a block of data and returns a fixed-size bit string. Hash value is sometimes called the message digest or simply digest. It is like a unique digital fingerprint of the data. This helps ensure that data has not been tampered with. Be wary that a birthday attack can happen if the same hash value is created for two different messages.
Hashing algorithms that exist are:
- MD2, MD4, MD5
- HAVAL
- SHA-0
- SHA-1
- SHA-224
- SHA-256
- SHA-384
- SHA-512
- RIPEMD-160
But how are hash algorithms put in use? Digital signatures can be hashed to verify that the document is encrypted with the user’s private key.
A Public Key Infrastructure uses user certificates. Certificate authorities would be like Symantec and Amazon web services. The registration authorities reviews the certificate authorities and tells the certificate authorities to issue keys to whom and supports functions to certificate authorities. The certificate revocation list is a list of certificates that are no longer valid.